Cryptocurrency Wallets Explained
Cryptocurrency wallets balance accessibility and security by separating hot and cold storage. Private keys and seed phrases prove ownership and enable recovery, yet exposure risks—phishing, backups, and device compromise—persist. The right wallet depends on use case, transaction tempo, and cross-chain needs, with attention to fees and interoperability. Robust security combines seed hygiene, multi-factor protections, and regular audits. Independent user control and disciplined key management are central, but practical tradeoffs remain, inviting careful consideration before committing.
How Wallet Types Work: Hot vs. Cold in Plain English
Hot and cold wallet types represent two ends of a spectrum in cryptocurrency storage, distinguished by where the private keys are kept and how often they are online. The analysis emphasizes risk implications, not romance.
Hot wallets enable rapid access; cold wallets prioritize security.
Common hot vs cold misconceptions mislead decisions, while wallet interoperability pitfalls can arise from incompatible formats and standards.
Private Keys and Seed Phrases: What You Own and What You Control
Private keys and seed phrases are the fundamental controls over digital assets, defining ownership and access without reliance on a centralized intermediary.
The analysis highlights that private keys grant direct authorization, while seed phrases enable recovery and portability.
Ownership control hinges on secure storage and disciplined handling, with recovery options presenting resilience against loss, theft, or device failure.
Risks: exposure, phishing, and backup compromise.
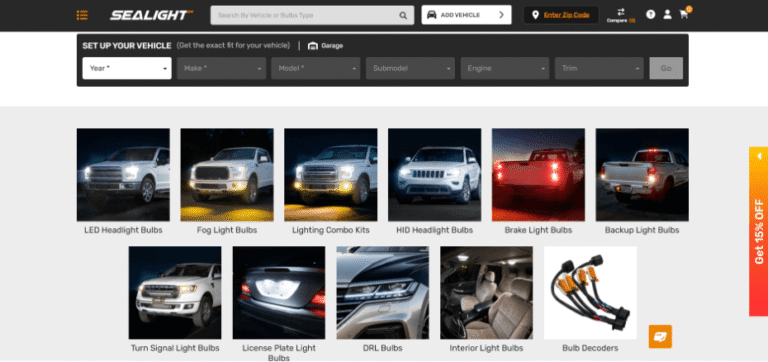
Choosing the Right Wallet for Your Use Case
Choosing the right wallet depends on the specific balance between security, accessibility, and recovery needs; investors should assess transaction frequency, asset diversity, and acceptable risk tolerance before selecting a form factor or architecture.
Practical selection hinges on wallet fees and cross chain interoperability, with emphasis on predictable costs, compatible assets, and the tradeoffs between control, convenience, and contingency planning for diverse use cases.
Security Best Practices to Keep Your Crypto Safe
With the prior emphasis on selecting an appropriate wallet form factor, the focus now shifts to practical security practices that minimize risk across holdings.
The analysis emphasizes structured risk reduction: hardware vaults, seed phrase hygiene, multi-factor protection, and regular software audits.
Privacy tradeoffs and wallet UX considerations frame choices, balancing usability with resilient defense, ensuring informed, independent ownership and reduced exposure to exploits.
Frequently Asked Questions
What Happens if I Lose My Device or Backup Phrase?
If a user loses a device or backup phrase, recovery is compromised; lost recovery phrases prevent access, and device loss strategies mitigate impact through redundant safeguards, risk-aware protocols, and governance for preserving ownership while maximizing freedom.
Can I Recover Funds Without the Original Private Key?
Yes, without the private key recovery is highly unlikely; recoverable funds generally depend on seed phrases or backups. The analysis shows private key loss makes access infeasible, underscoring substantial risk and emphasizing robust backup practices for freedom-seeking users.
Do Wallets Support Multi-Currency or Cross-Chain Assets?
Cross chain compatibility exists variably; wallets often support multi currency across networks, but true universal cross-chain transfers remain limited. Analysts warn risk of fragmented standards, security gaps, and dependence on bridging services, affecting freedom-oriented users’ strategic asset management.
See also: Cryptocurrency Basics for Beginners
Are There Fees to Interact With Non-Custodial Wallets?
Yes, there are fees to interact with non-custodial wallets. The analysis notes variability: on-chain transactions incur network fees, while non custodial wallets may impose optional or indirect costs from integrations, speed choices, and liquidity access, influencing risk-adjusted cost efficiency.
How Do Wallets Handle Backups for Hardware Devices?
Backups for hardware wallets rely on seed phrases and hardware ciphered storage; analysts cite multi-device redundancy as key. Anecdote: a vault’s split-key approach mirrors backup strategies, illustrating resilience. Emphasize hardware encryption, risk-aware, freedom-preserving design.
Conclusion
Conclusion (satirical, data-driven, risk-aware, third-person): In the grand theater of crypto, wallets perform with cold precision and hot bravado, while private keys wink from behind firewalls. The data shows cost, speed, and cross‑chain frictions matter more than romance. Yet the risk banner never folds: phishing, backups, and single‑point failures loom. The conclusion is plain arithmetic: empower control, insist on backups, and audit relentlessly. Otherwise, ownership remains a rumor wrapped in a seed phrase, sung to the tune of fees.